Empowering Healthcare Heroes with Cutting-Edge IT Solutions
What is the difference?
Every IT company list healthcare and dental as a supported industries. We do nothing but healthcare and dental!
Vital IT was created by people who managed large hospital IT, moved healthcare data centers, PACS admin and all things healthcare IT. No one in the industry has the same credentials.
Welcome to Vital IT, where we're bringing unparalleled healthcare technology consulting and IT support exclusively to medical and dental offices. As a unique force in the United States healthcare sector, we're here to ensure your practice not only thrives but leads in efficiency, security, and compliance.

YEARS OF EXPERIENCE IN HEALTHCARE & DENTAL
Why Choose Vital IT?
We answer the phone when you call.
You get our unequaled expertise at a fraction of the cost. All of our services are one low monthly cost. Not a bunch of nickel and dime add ons.
We help you solve business problems through technology.
Since we specialize in only medical and dental providers. We draw on our experience with hundreds of providers to help you get the most from your business.
Your systems stay secure so you can sleep at night and focus on your patients.
Do you like saving money? We audit and negotiate rates on your IT services.
We help with connected medical systems like X-Ray, ultrasound, PACS, EMR, lab and more.
You can rely on us for everything IT including VOIP phones, vendor management, and of course top notch support so you can focus on what you do best.
Vital IT can help you with adding value for your staff and patients through utilizing systems and processes designed specifcally for you.
SAVE MONEY, SAVE TIME, STAY SECURE & COMPLIANT, GET RID OF TECH HEADACHES!






BLOG POSTS
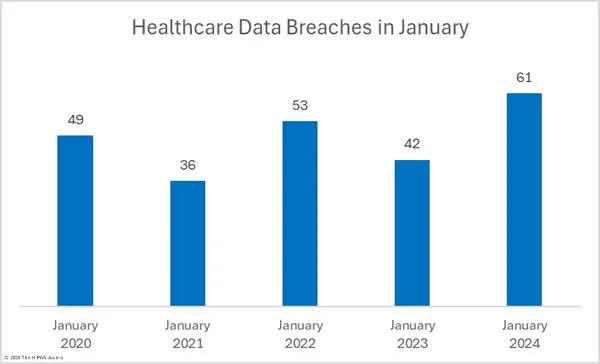
Healthcare hacking on the rise in 2024
The Growing Threat of Cyber Attacks in Healthcare
In recent years, the healthcare industry has become an increasingly attractive target for cybercriminals. The rise in cyber attacks on healthcare organizations poses a significant threat not only to the institutions themselves but also to the patients they serve. As healthcare providers continue to digitize their operations and rely more heavily on interconnected systems, the urgency to address cybersecurity vulnerabilities becomes paramount.
The Unique Vulnerabilities of Healthcare
Healthcare organizations are particularly vulnerable to cyber attacks for several reasons:
Valuable Data: Medical records contain a wealth of sensitive information, including personal identification details, medical histories, and financial information. This makes them highly valuable on the black market, often fetching higher prices than other types of data.
Complex Networks: Hospitals and clinics operate on complex, interconnected networks that include a variety of devices such as computers, medical equipment, and mobile devices. This complexity increases the number of potential entry points for cybercriminals.
Legacy Systems: Many healthcare organizations still rely on outdated software and legacy systems that are not designed to withstand modern cyber threats. These systems can be difficult to update or replace due to compatibility issues and the potential impact on patient care.
Resource Constraints: Budget constraints and a lack of dedicated IT security personnel can leave healthcare organizations ill-prepared to defend against sophisticated cyber attacks. Smaller practices, in particular, may struggle to allocate sufficient resources to cybersecurity.
Common Types of Cyber Attacks in Healthcare
Several types of cyber attacks are prevalent in the healthcare sector:
Ransomware: Ransomware attacks involve encrypting an organization's data and demanding a ransom payment for its release. These attacks can cripple healthcare providers, disrupting patient care and leading to significant financial losses.
Phishing: Phishing attacks use deceptive emails or messages to trick employees into revealing sensitive information or downloading malware. Given the high volume of email traffic in healthcare settings, these attacks can be particularly effective.
Insider Threats: Insider threats occur when employees or contractors misuse their access to sensitive information. This can be due to malicious intent or simple negligence, such as mishandling patient data.
Distributed Denial of Service (DDoS): DDoS attacks overwhelm a network with traffic, causing system slowdowns or outages. These attacks can disrupt operations and prevent access to critical systems and data.
The Impact of Cyber Attacks on Healthcare
The consequences of cyber attacks on healthcare organizations can be severe:
Patient Safety: Cyber attacks can disrupt the delivery of care, leading to delayed or canceled procedures, and potentially jeopardizing patient safety. In extreme cases, attacks can result in life-threatening situations.
Financial Losses: The costs associated with cyber attacks can be staggering. These include ransom payments, legal fees, regulatory fines, and the expense of recovering and securing systems. Additionally, organizations may face lost revenue due to operational downtime.
Reputational Damage: A breach can erode trust in a healthcare provider, damaging its reputation and leading to a loss of patients. Rebuilding trust after a cyber attack can be a lengthy and challenging process.
Regulatory Consequences: Healthcare organizations are subject to strict regulations regarding data protection, such as HIPAA in the United States. A breach can result in significant penalties and increased scrutiny from regulatory bodies.
Strategies for Mitigating Cyber Threats
To combat the growing threat of cyber attacks, healthcare organizations must adopt comprehensive cybersecurity strategies:
Employee Training: Regular training programs can help employees recognize and respond to cyber threats, such as phishing attempts. Awareness and education are critical components of an effective cybersecurity strategy.
Robust Security Measures: Implementing strong security measures, such as multi-factor authentication, encryption, and intrusion detection systems, can help protect sensitive data and prevent unauthorized access.
Regular Updates and Patching: Ensuring that all software and systems are up-to-date with the latest security patches can mitigate vulnerabilities. This includes replacing legacy systems that cannot be adequately secured.
Incident Response Plans: Developing and regularly testing incident response plans can help organizations respond quickly and effectively to cyber attacks, minimizing damage and downtime.
Third-Party Security Assessments: Engaging third-party experts to conduct security assessments can provide an objective evaluation of an organization’s cybersecurity posture and identify areas for improvement.
Conclusion
The growing threat of cyber attacks in healthcare demands urgent and sustained attention. As the industry continues to evolve and digitize, healthcare organizations must prioritize cybersecurity to protect their patients, data, and operations. By adopting proactive measures and fostering a culture of security awareness, healthcare providers can better defend against the relentless threat of cybercrime.
About Vital IT
We are the premier IT Service for HealthCare and Dental Providers.
Our services are available in the U.S.
Contact:
888-757-5088
info@vitalitpros.com
Hours Of Operation
M-F 8:00 AM - 5:00 PM